OWASP Top 10
A regularly updated list of the most critical security risks to web applications
Open Worldwide Application Security Project (OWASP) is a community-led security project.
The team is made up of security experts from around the world.
Broken Access Control
Any situation where a user can access something that is outside their intended permissions
Manipulating URLs, cookies or tokens
Missing access controls on unexpected HTTP methods or routes
/api/getCustomerInformation?id=123129112
Cryptographic Failures
Bad cryptography that can lead to unexpected data exposure
Weak SSL / TLS configurations that allow person in the middle attacks
Missing HTTP Strict Transport Security headers that allow HTTP downgrade attacks
The use of default passwords or secrets in applications
Keys using weak algorithms or low entropy
Accidental key exposure
Injection
Situations where user supplied data is directly injected into your code
Not just SQL!
LDAP, NoSQL, system commands, and ORMs are all targets.

Insecure Design
Design and architectural flaws in your system
Promotes secure by design and ensures teams understand the security implications of changes

Security Misconfiguration
Applications that are improperly secured because of a misconfiguration
Missed steps in go live or hardening documentation
Applications deployed to production with development configurations
Features enabled that aren't being used increasing the attack surface area

Vulnerable and Outdated Components
Applications using components with known security vulnerabilities
Both accidental vulnerabilities and malicious changes apply here
Supply chain attacks
Identification and Authentication Failures
Allowing the wrong user (malicious or not) to authenticate to a system
Account enumeration, especially when weak and previously leaked passwords are allowed
Misconfiguration of authentication that allows MFA bypass, OAuth scope creep, unverified user registrations, etc..
Software and Data Integrity Failures
Assuming that the build you just tested is the one that will be deployed
Using dependencies from third parties without verifying them
Allowing untrusted code into your ecosystem

Security Logging and Monitoring Failures
Not having enough information to investigate an issue
Logging so much information that it becomes toxic waste

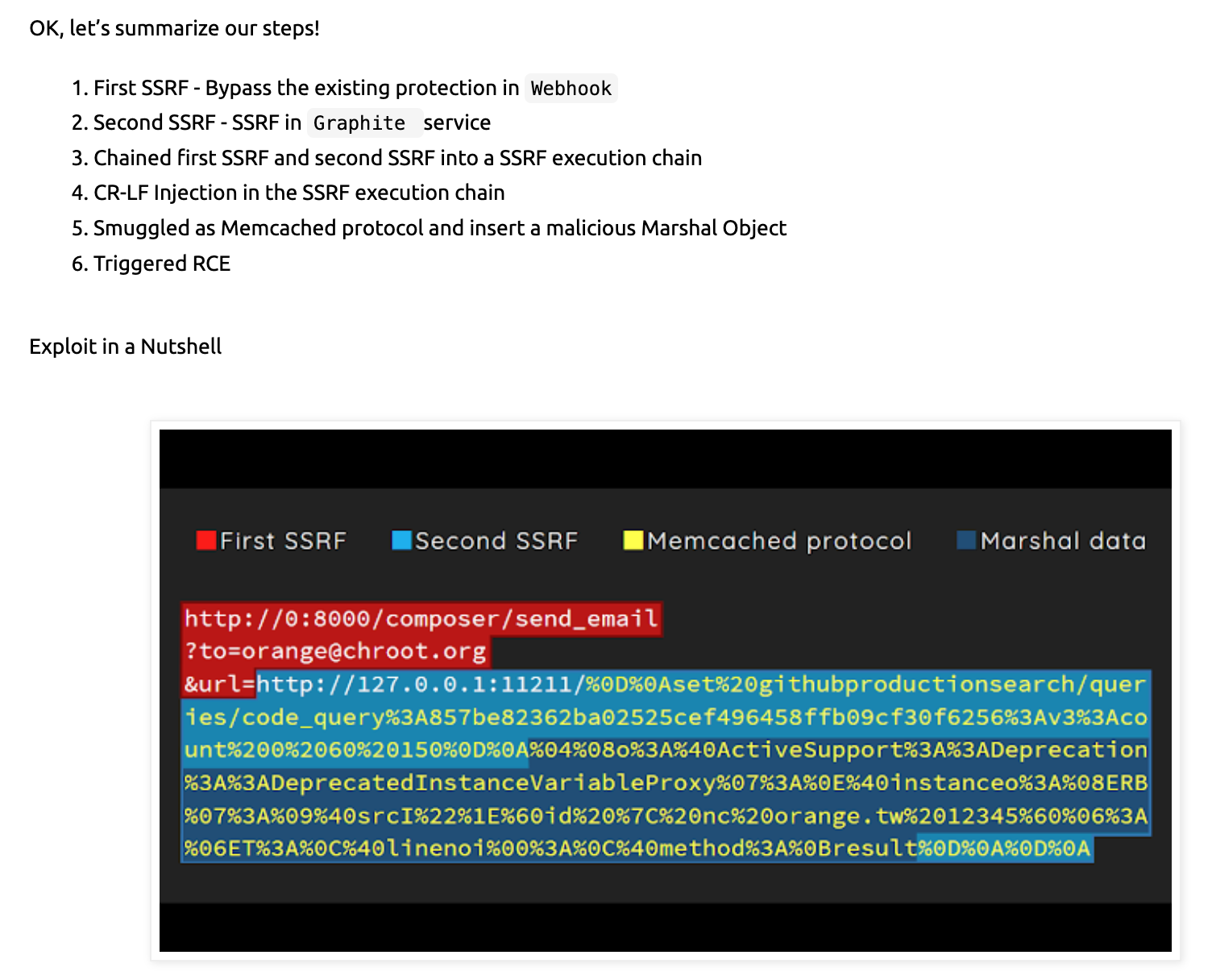
Server-Side Request Forgery
Allowing your server to make requests to a resource provided by a user
Making requests that reveal metadata about the service
Tricking servers into mining cryptocurrencies
http://google.com:80+&@127.88.23.245:22/#+@google.com:80/
http://0/
Wrap Up
The OWASP Top 10 is a great guide, but is really only the first 10 of 100s of potential issues
Think about security early, during the planning and design phase of new work
Resources if you want to learn more
Exposure links
🙏🏻 Thanks!